Hello Everyone,
We’re sending this out to educate you about the risk of malware—malicious software—and virus prevention best practices. The best way to understand how to avoid malware is understanding how infections occur, what different types of infections do, and the most common virus prevention practices.
General Ways Infections Occur:
There are too many ways a machine can get infected to describe here, and new ways to infect machines are discovered every day, so we’ll just cover the most common.
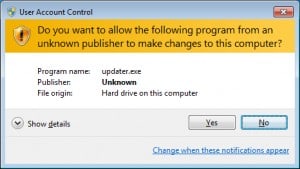
Accepting User Account Control prompts without reading them.
- Everyone has seen these annoying boxes that pop up every time you want to run certain files. They do, however, serve a very important purpose: to make sure you understand what is happening on your machine at all times.
- Best Practice: If there is no Publisher, like the example below, do not run it. All reputable software vendors will associate their name with their software.
 E-mail Attachments and Links in Emails
E-mail Attachments and Links in Emails
- Phishing e-mails are the most common way businesses get infections. Phishing
e-mails can be hard to spot, but there is usually something off about them. - Common Phishing E-mail Content: (This list is not exhaustive by any means.)
- Fake FedEx or UPS orders.
- Password reset prompts you didn’t request.
- Requests to update software. Software isn’t updated over e-mail.
- E-mails spoofed to look like they are coming from someone trustworthy.
- Often indicates the person who it came from has an infection that is sending out spam on their machine. Please warn that person ASAP. At this point, everyone’s e-mail is probably close to being blacklisted, which will stop everyone’s e-mail from flowing out.
- Best Practice: Don’t open or click on anything that you did not request. Hover your cursor over links in e-mails to see where they go before clicking on them. Spoofing a link to download a file is very easy. If the URL it’s actually pointed at looks strange, don’t click it.

Unpatched Machines
- Updates are time-consuming, but most updates to software are security updates, so it’s very important to stay up-to-date.
- Java, Adobe Flash Player, and Adobe Reader are legitimate programs that have many uses and are often necessary to do many tasks online. However, due to the fact that these are installed on so many machines worldwide, malware creators use these programs the most to find ways into machines. It is extremely important to keep these programs as up-to-date as possible. Each update has many security patches to protect your system.
- The second Tuesday of every month is patch day for Windows. Microsoft releases many security fixes every month for newly found vulnerabilities.
- Best Practice: Update your software whenever you can or whenever you see the bubbles pop up on the bottom right in the system tray. Run Windows updates when you hear the tornado siren test and reboot your machine before leaving for the day.
Downloading Infected Software
- These are harder to spot as even programs that do “legitimate” things can have malicious code in them (i.e. games, utilities, demos, etcetera). Often you may end up with a program that does what it’s supposed to do, but has opened your computer up to additional vulnerabilities.
- This happens most often when pirating software, music, or movies. Obviously this is illegal in and of itself, as well.
- Best Practice: Stick to reputable websites, don’t download programs from sketchy/random websites. If it feels strange or too good to be true, it is. Be skeptical of everything!
Common Types of Malware:
Adware:
- Created to send unwanted advertisements to the computer that is infected.
- You’ll recognize them as pop ups.
Bots:
- Software created to perform actions in the background without alerting the machine’s operator to what is being done.
- You’ll probably only notice your machine running slower than normal if there is a bot on your machine. This is where botnets (bot networks) come from. They are often used in part of attacks on websites, mine virtual currency, or generate ad click revenue.
Ransomware:
- These are designed to hold the machine or data hostage for a fee.
- Most recently CryptoLocker started infecting many business via phishing e-mails, encrypting files and holding them for ransom.
- The only way to recover from these are to restore from a backup, rebuild the machine, or pay the ransom. Paying isn’t a guaranteed way to get your data back, though. Often they’ll just take your money.
Rootkits:
- These are designed to be very stealthy and are extremely difficult to remove once on a machine.
- Allow the creator of the software to remotely access the machine, join it to a botnet, install other malware, or change the system configuration.
- For bad Rootkits, an infected machine may just have to be wiped and rebuilt.
Spyware:
- Using key loggers, these track what you’re typing to steal personal information (i.e. usernames, passwords, ssn, credit card numbers, etcetera).
Trojans:
- Trojans are designed to look like a legitimate program to trick people into downloading and installing them.
Prevention:
Other than the best practices stated above, antivirus programs and firewalls are used to protect networked machines from viruses, but they are by no means foolproof.
Antivirus:
- Real-time protection programs like Microsoft Security Essentials, Norton Antivirus, and McAfee examine files and programs as they are running on the machine and compare them to their definitions.
- Definitions are updated nearly daily with new signatures of malware found active in the “wild.” If a program running on the system matches one of the antivirus’ definitions, it blocks it from running any further and scans the machine for the source and any additional infections.
- These programs will protect from most viruses, but are not perfect and often miss infections, especially newly released malware that has yet to have a definition.
- Antivirus programs will also let things through that you request. So, if you requested a program that is infected to install, your antivirus WILL let it through.
Firewalls:
- A firewall is a piece of hardware or software that is used to create a barrier between the local network and the outside internet.
- It filters traffic by inspecting every packet (piece of information) that is coming in and going out of the network. If the packet doesn’t meet certain requirements, it isn’t allowed into the network.
- The purpose of a firewall is to protect from random attacks that occur on the open internet every second. The usual statistic quoted here is that an unpatched machine sitting on the open internet (not behind a firewall) will be found and infected in less than 10 minutes by programs that are constantly scanning, looking for new machines to infect.
- Just like antivirus programs, firewalls WILL allow traffic through if you have requested it.
Although antivirus and firewalls are there to protect your machine, the only real defense is you. Neither firewalls nor antivirus programs will stop everything and they will allow traffic though regardless of its danger if you request it. You are the first and last line of defense. Be skeptical of everything and remain vigilant.
Thank You,
TSTS Team